Microsoft released its latest Windows 10 update that boasts of numerous improvements. However, the changes bring about a new form of security threat for the freshly updated Microsoft Windows 10 operating system. Since Microsoft had announced the aforementioned update on May 21st, it is safe to assume that the update would still need a couple of days to be more widespread.
 The update brings new things to the table such as Windows Sandbox and refreshes the Start menu to be simpler on newer devices. Microsoft with this updated software brings a change in the manner Windows 10 handles reserved storage. Furthermore, Cortana has now been moved from the search tab as well.
The update brings new things to the table such as Windows Sandbox and refreshes the Start menu to be simpler on newer devices. Microsoft with this updated software brings a change in the manner Windows 10 handles reserved storage. Furthermore, Cortana has now been moved from the search tab as well.
Microsoft has been known to have a passive approach to the release of their software updates, hence most users would not be receiving the said update immediately. To check if the update is available clicking on the Windows Update option under Update and Security can be found in the System’s Settings.

Zero-Day vulnerability or 0-Day vulnerability, for those not aware of technical jargons, is a computer vulnerability that has not been discovered by the vendor or main party in concern (here Microsoft). The classification remains until the main party acknowledges the issue that can be abused by exploiters/hackers.
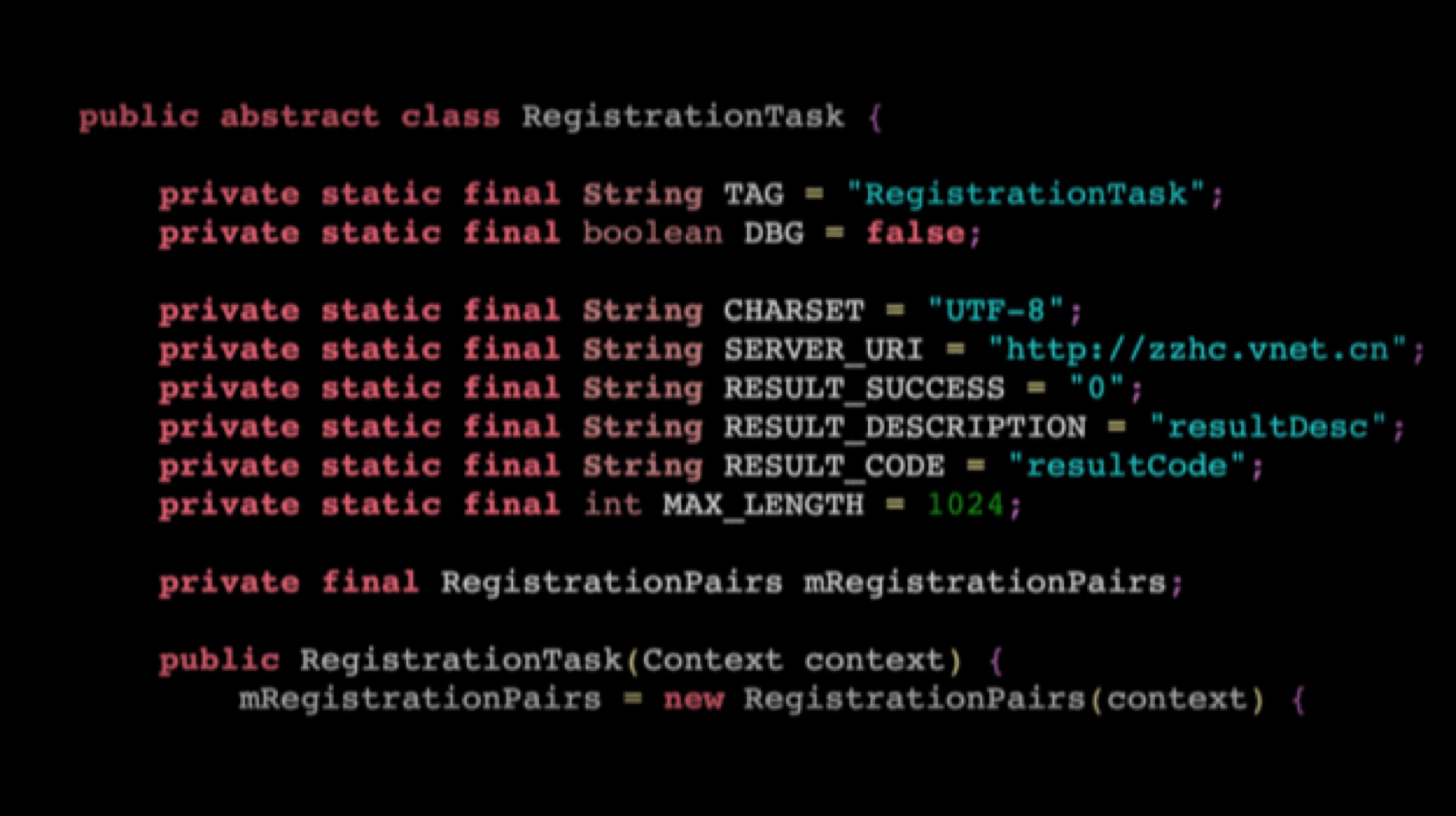
A researcher named SandboxEscaper published the exploit code on GitHub and released a video of how the exploit can be abused. SandboxEscaper has been known to have discovered other such zero-day exploits. The vulnerability in question targets the local privilege escalation (LPE) that allows third-party complete access to the machine by granting them administrator status over the actual user. In other words, a users computer may be remotely accessed by those who seek to gain access.
Also Read: Xiaomi Black Shark 2 To Be Retailed Via Flipkart In India, Launching On 27 May
The zero-day cannot be exploited in and of itself but paves the way for other methods to have more of an effect when used simultaneously. SandboxEscaper reports that the Windows Task Scheduler is the vulnerability that makes the exploit possible. If the hacker used a particular .job file in the Windows Task Scheduler after gaining access to the computer, it grants administrator access to the system giving the hacker unwarranted power to change fundamental settings on the PC.





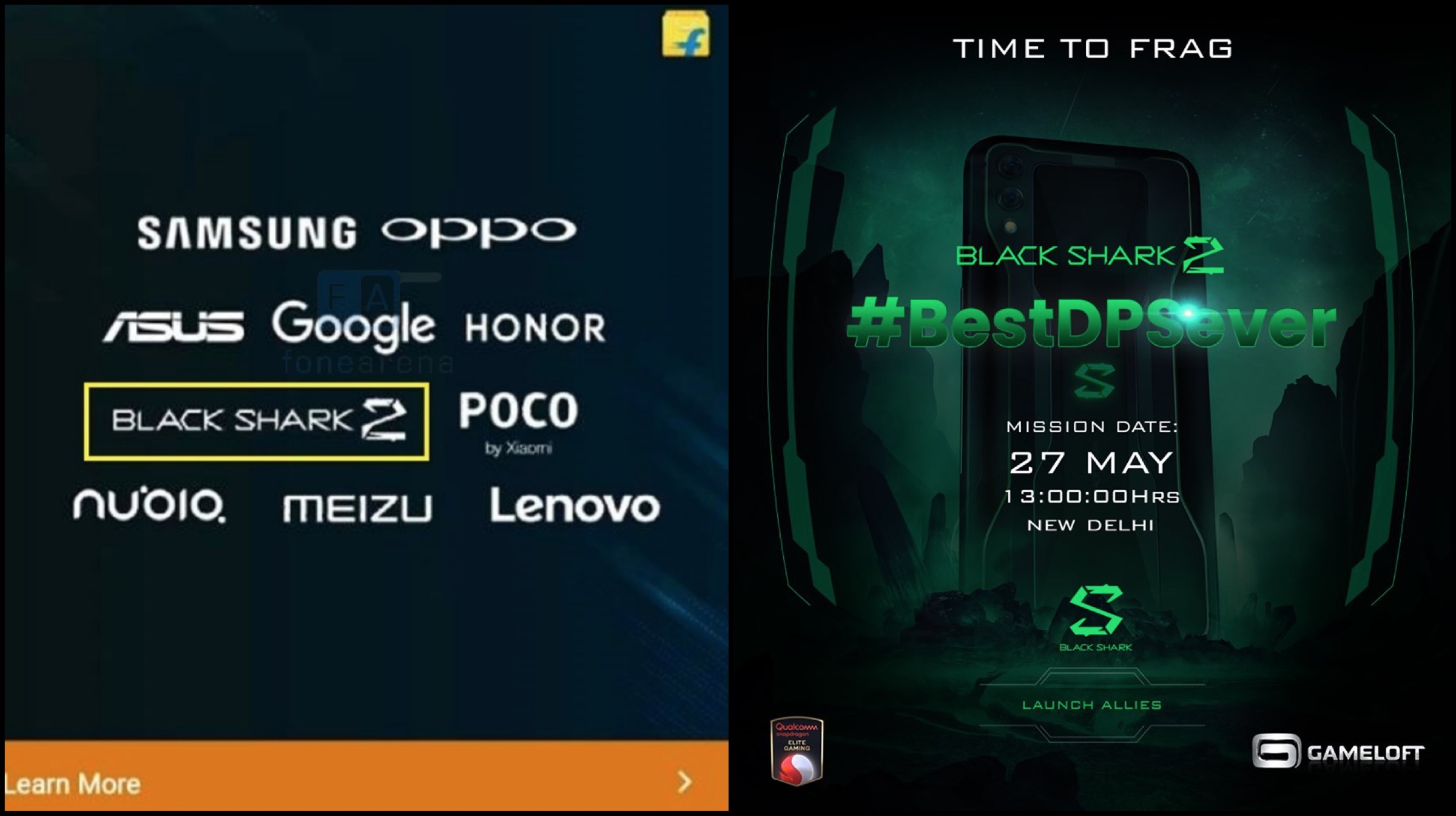 The Black Shark 2 has a modern design with a distinctive design on the rear and a large screen display on the front. The smartphone measures 163.61 x 75.01 x 8.77 mm and weighs in at 205 grams. It sports a 6.39 inch AMOLED display which is surrounded by thin bezels on all sides. The smartphone’s display has a resolution of 2340 x 1080 px and a pixel density of 403 ppi. The display panel can reach brightness levels of upto 430 nits and has an aspect ratio of 19.5:9.
The Black Shark 2 has a modern design with a distinctive design on the rear and a large screen display on the front. The smartphone measures 163.61 x 75.01 x 8.77 mm and weighs in at 205 grams. It sports a 6.39 inch AMOLED display which is surrounded by thin bezels on all sides. The smartphone’s display has a resolution of 2340 x 1080 px and a pixel density of 403 ppi. The display panel can reach brightness levels of upto 430 nits and has an aspect ratio of 19.5:9. Noteworthy, the AMOLED display also supports pressure sensitive controls which means the amount of pressure applied to the screen while playing games would affect the on-screen controls. For securely and swiftly unlocking the device it also features an on display fingerprint sensor. Talking further about the design of the Xiaomi Black Shark 2, its right side houses the power button and a shark slider which when toggled turns on gaming mode for optimized performance while the left side houses the volume rockers. The bottom of the device accommodates the USB Type-C port. To keep the temperature of the device under check during game-intensive sessions, it also has a vapour cooling chamber.
Noteworthy, the AMOLED display also supports pressure sensitive controls which means the amount of pressure applied to the screen while playing games would affect the on-screen controls. For securely and swiftly unlocking the device it also features an on display fingerprint sensor. Talking further about the design of the Xiaomi Black Shark 2, its right side houses the power button and a shark slider which when toggled turns on gaming mode for optimized performance while the left side houses the volume rockers. The bottom of the device accommodates the USB Type-C port. To keep the temperature of the device under check during game-intensive sessions, it also has a vapour cooling chamber. As mentioned before, the rear of the Xiaomi Black Shark 2 has a unique design with green coloured decals that run along the sides of the smartphone. The rear panel also harbours the company logo and dual camera setup. The dual camera setup consists of a 48 MP sensor, 12 MP sensor and an LED Flash which can also capture 2160p videos at 30 fps. It also has a 20 MP front-facing selfie camera which is placed in the bezel above the display. The front camera can also capture 1080p videos at 30 fps.
As mentioned before, the rear of the Xiaomi Black Shark 2 has a unique design with green coloured decals that run along the sides of the smartphone. The rear panel also harbours the company logo and dual camera setup. The dual camera setup consists of a 48 MP sensor, 12 MP sensor and an LED Flash which can also capture 2160p videos at 30 fps. It also has a 20 MP front-facing selfie camera which is placed in the bezel above the display. The front camera can also capture 1080p videos at 30 fps.  Under the hood, the Black Shark 2 runs on the Snapdragon 855 SoC which consists of an octa-Core CPU with the Adreno 640 GPU. The smartphone is powered by a huge 4,000 mAh battery which supports fast charging upto 27 W. Connectivity options on the device include 802.11 ac Wi-Fi, Bluetooth 5.0, Dual 4G VoLTE and GPS.
Under the hood, the Black Shark 2 runs on the Snapdragon 855 SoC which consists of an octa-Core CPU with the Adreno 640 GPU. The smartphone is powered by a huge 4,000 mAh battery which supports fast charging upto 27 W. Connectivity options on the device include 802.11 ac Wi-Fi, Bluetooth 5.0, Dual 4G VoLTE and GPS. 










 The updated Google lens has a new slide-up menu that houses circular buttons with a variety of functionalities. The older buttons that were previously used to scan barcodes/QR codes and Copy Text have been sacrificed to bring in new buttons. The first button will allow the user to directly overlay the translated text in their own language, without opening the Translate application. The second button is again familiar to a lot of users, which allows them to copy the text in an image and paste it elsewhere.
The updated Google lens has a new slide-up menu that houses circular buttons with a variety of functionalities. The older buttons that were previously used to scan barcodes/QR codes and Copy Text have been sacrificed to bring in new buttons. The first button will allow the user to directly overlay the translated text in their own language, without opening the Translate application. The second button is again familiar to a lot of users, which allows them to copy the text in an image and paste it elsewhere. Also Read:
Also Read: 








 G Suite is the business/corporate version of Google’s Gmail and other Google related applications. Reportedly the bug was born out of a feature that was made specifically for companies, namely the Administrators to reset any user passwords or accounts for newly recruited employees. This process had the Admin console store the passwords in plain text instead of being encrypted. Google has since removed this function for Administrators.
G Suite is the business/corporate version of Google’s Gmail and other Google related applications. Reportedly the bug was born out of a feature that was made specifically for companies, namely the Administrators to reset any user passwords or accounts for newly recruited employees. This process had the Admin console store the passwords in plain text instead of being encrypted. Google has since removed this function for Administrators. Google has a relatively good track record of detecting bugs and glitches in their system, but this bug points a finger towards a myriad of tech giants and social media companies as well such as
Google has a relatively good track record of detecting bugs and glitches in their system, but this bug points a finger towards a myriad of tech giants and social media companies as well such as 








 Zen Mode is a feature that basically locks a user out of his/her device for 20 minutes. The user will not see/hear any notifications on the device, and at the same time, applications will be unusable as well. The only two features that are accessible is the call application and the camera. In case users decide to turn off Zen Mode before the time period of 20 minutes, they are out of luck, since no workaround will disable Zen Mode. Even restarting the OnePlus 7 Pro doesn’t help, as the Zen Mode timer continues from the same point you left it on.
Zen Mode is a feature that basically locks a user out of his/her device for 20 minutes. The user will not see/hear any notifications on the device, and at the same time, applications will be unusable as well. The only two features that are accessible is the call application and the camera. In case users decide to turn off Zen Mode before the time period of 20 minutes, they are out of luck, since no workaround will disable Zen Mode. Even restarting the OnePlus 7 Pro doesn’t help, as the Zen Mode timer continues from the same point you left it on.  The screen recorder, on the other hand, allows native recording (in the same number of frames per second) of the screen’s display without any overlay or watermark. Gamers can record their gaming sessions and export them, or users can create how-to videos for conveying specific information. As per reports, some OnePlus users side loaded these two applications into their older devices, which didn’t function as desired. For instance, sound capture was disabled during screen recording and Zen Mode was still allowing notifications to push through.
The screen recorder, on the other hand, allows native recording (in the same number of frames per second) of the screen’s display without any overlay or watermark. Gamers can record their gaming sessions and export them, or users can create how-to videos for conveying specific information. As per reports, some OnePlus users side loaded these two applications into their older devices, which didn’t function as desired. For instance, sound capture was disabled during screen recording and Zen Mode was still allowing notifications to push through.




