PlayDrone Discovers a Serious Security Breach in Google Play

By developing a new tool called PlayDrone, Jason Nieh, professor of computer science at Columbia Engineering, and PhD candidate Nicolas Viennot reported that they have discovered a crucial security problem in Google Play – the official Android app store where millions of Android users get their apps.
PlayDrone uses hacking techniques to find a way around Google’s security to download Google Play apps, and then recover and analyse their sources. It scales down by simply adding more servers and in this way, it manages to compile over 880,000 of the 1.1 million free apps it downloads.
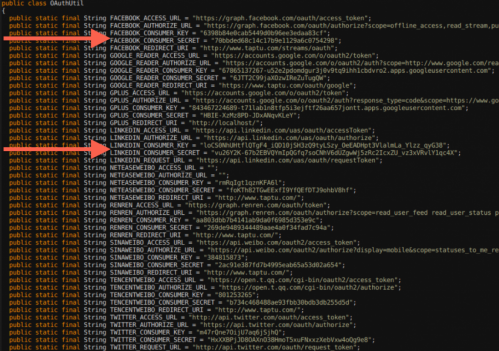
While analyzing this, it was found that developers often store their secret keys of their app’s software similar to username and password data, which can be further used to steal user data or resources from entities such as Amazon and Facebook.
Even the “Top Developers” promoted by Google Play have included these vulnerabilities in their apps. These vulnerabilities can affect users even if they are not actively running the Android apps.
This tool, Playdrone, not only revealed this security loophole but also used it to provide insight into Android apps and improve the quality of Google Play. For example, the tool also found that roughly 25 percent of all free apps on Google Play are clones of other apps. This information could be used to help Google crack down on cloned content, which would be great news for developers who are creating original apps. Google Play has more than one million apps and over 50 billion app downloads.
It also performed an analysis of the 10 best rated and 10 worst rated apps on the Google Play store, and found that even the worst-rated app has over a million downloads. Google is now using the techniques to scan all the apps for such problems to prevent this from happening again in the future.