Apple Has Successfully Fixed The Eavesdropping FaceTime Bug

Last week was a tough one for Apple, as iOS devices were hit by a major bug in the Facetime application. Furthermore, a Facebook project was caught spying on users that violated Apple’s Enterprise Developer Program policies. Fortunately, Apple was able to revoke Facebook’s enterprise certificate on its devices that halted the cruel project.
What Is The Eavesdropping Bug?
Last week a 14-year old high school student from the US discovered a bug on Apple’s iOS devices that ran on iOS 12. The teenager discovered that iOS 12 devices would allow users to listen to another FaceTime user by calling them and adding themselves to a group call before the contact answered. This case caused a huge stirrup as iOS devices were previously considered significantly secure than its Android counterparts.
Apple’s Solution
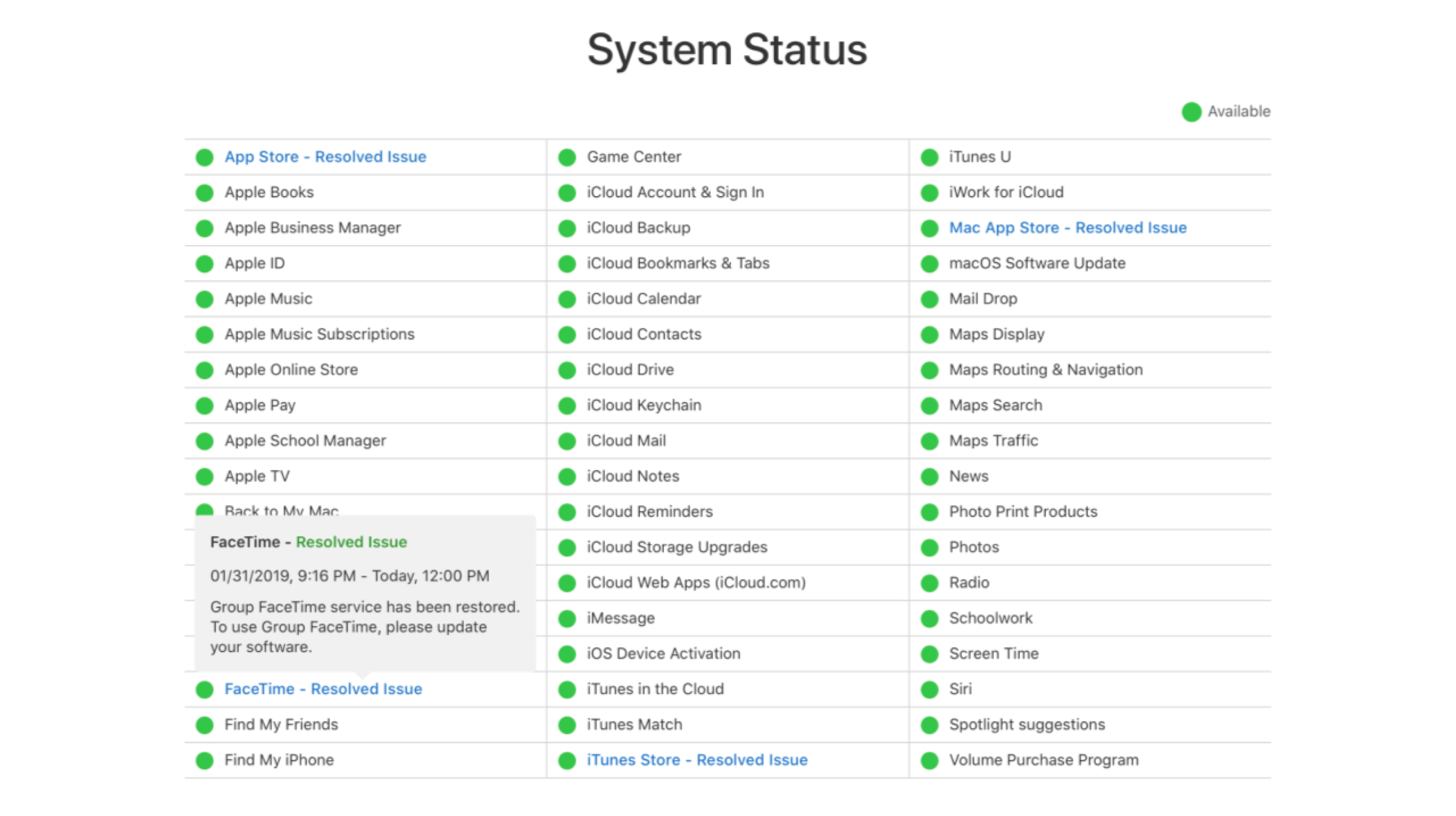
After the eavesdropping bug was originally discovered, Apple manually disabled the servers that allowed FaceTime connectivity. Apple has released iOS 12.1.4 update for iPhone, iPod Touch and iPad that has successfully fixed the FaceTime bug. Also, the FaceTime servers have now been reset and are functioning properly.
Google’s Shocking Revelations
CVE-2019-7286 and CVE-2019-7287 in the iOS advisory today (https://t.co/ZsIy8nxLvU) were exploited in the wild as 0day.
— Ben Hawkes (@benhawkes) February 7, 2019
Also Read: AMD Has Launched The World’s First 7nm Based GPU, Radeon VII In India
After the iOS 12.1.4 update, an apex Google security engineer, Ben Hawkes on his Twitter revealed that the new update has also fixed two vulnerabilities. Shockingly, the executive claimed that both the vulnerabilities were exploited in the wild as zero-day. A zero-day vulnerability is a software, hardware or firmware flaw unknown to the manufacturer until hackers leverage that flaw to conduct a cyber attack.